530a3 | Information Systems homework help
Case Project 5-1:
Configuring Encryption in Word 2010The chief information officer (CIO) in your organization has expressed concerns about the use of encryption by employees. Currently, users encrypt Microsoft Word documents using the built-in encryption function. The CIO has been considering a third-party cryptographic product but needs more information about how Word encryption works before she can make an informed decision. You have been asked to write a two-page report that explains the extent to which the IT department can configure the cryptographic features of Word2010. What is the process involved in configuring encryption?
Case Project 5-2: Using DNSSEC You are employed by an e-commerce company as an assistant to the chief security officer. Your company has received a number of recent complaints from customers who have ordered products but have not received them. In addition, many of these customers have reported being victims of identity theft. Your company’s legal department has recommended that all departments study their practices to ensure that they are taking reasonable measures to prevent identity theft. The chief security officer believes that DNS cache poisoning attacks may be responsible for traffic being redirected from your company’s Web site to impostorWeb sites where customer information is then collected and misused. You have been asked to prepare a two-page report that explains how DNS cache poisoning attacks work and how the DNSSEC system can help to prevent these attacks.
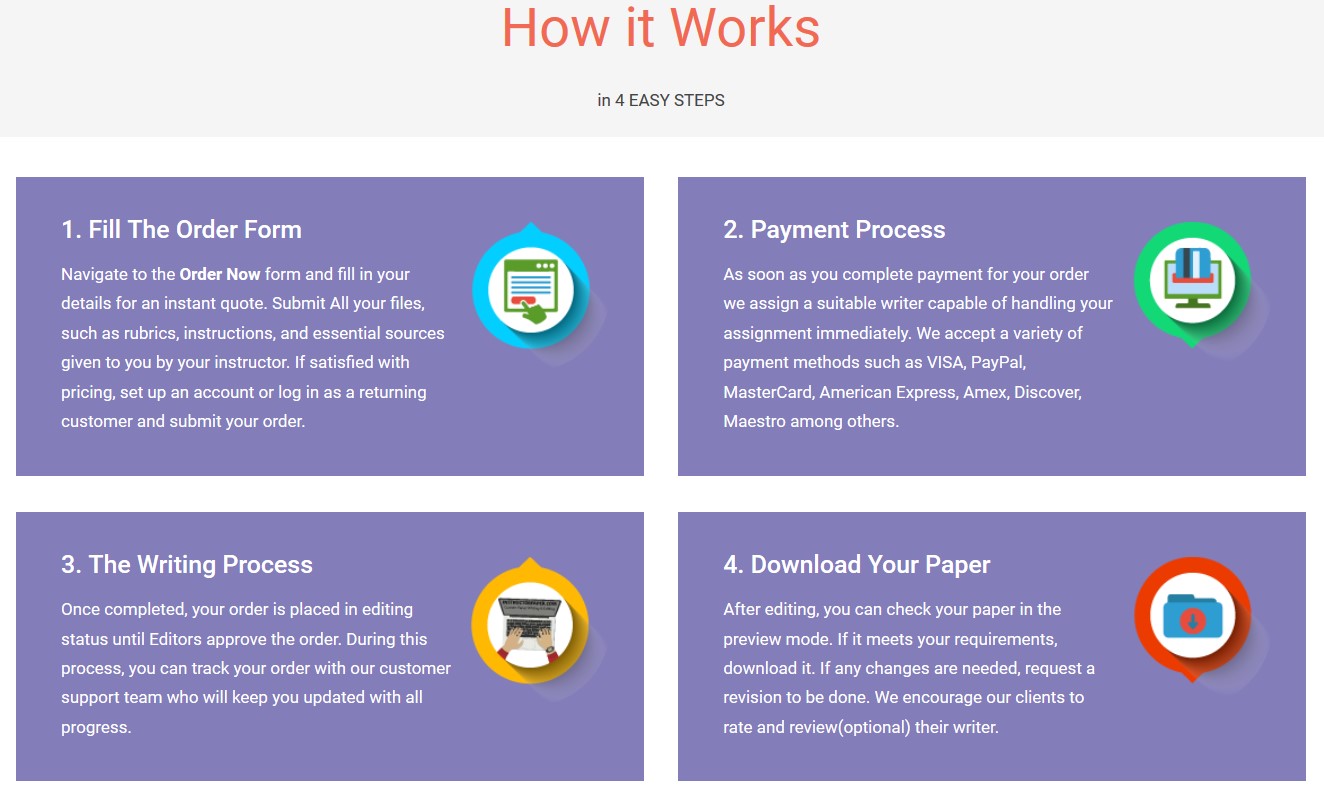
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper Now"If this is not the paper you were searching for, you can order your 100% plagiarism free, professional written paper now!"