Assignment 9
Use the template attached, to finish the assignment:Discuss the differences between external and internal threats as they relate to network security. Which threat is most difficult to defend against and why? What protections would be used specifically related to internal threats? Why is it important for organizations to have a written security policy?Highlight the basic functions and operation of public key cryptography. What is the “Advanced Encryption Standard”? How are digital signatures generated and used?Discuss “Pretty Good Privacy.” What is it? Why has it stood the test of time, and will it be good enough in the future, why or why not? Compare it to Kerberos encryption.Identify and compare the two primary and currently used techniques to secure wireless communications. How safe are your data communications when using a typical wireless hotspot (public)? What can you do to improve your data security when using one of these services?
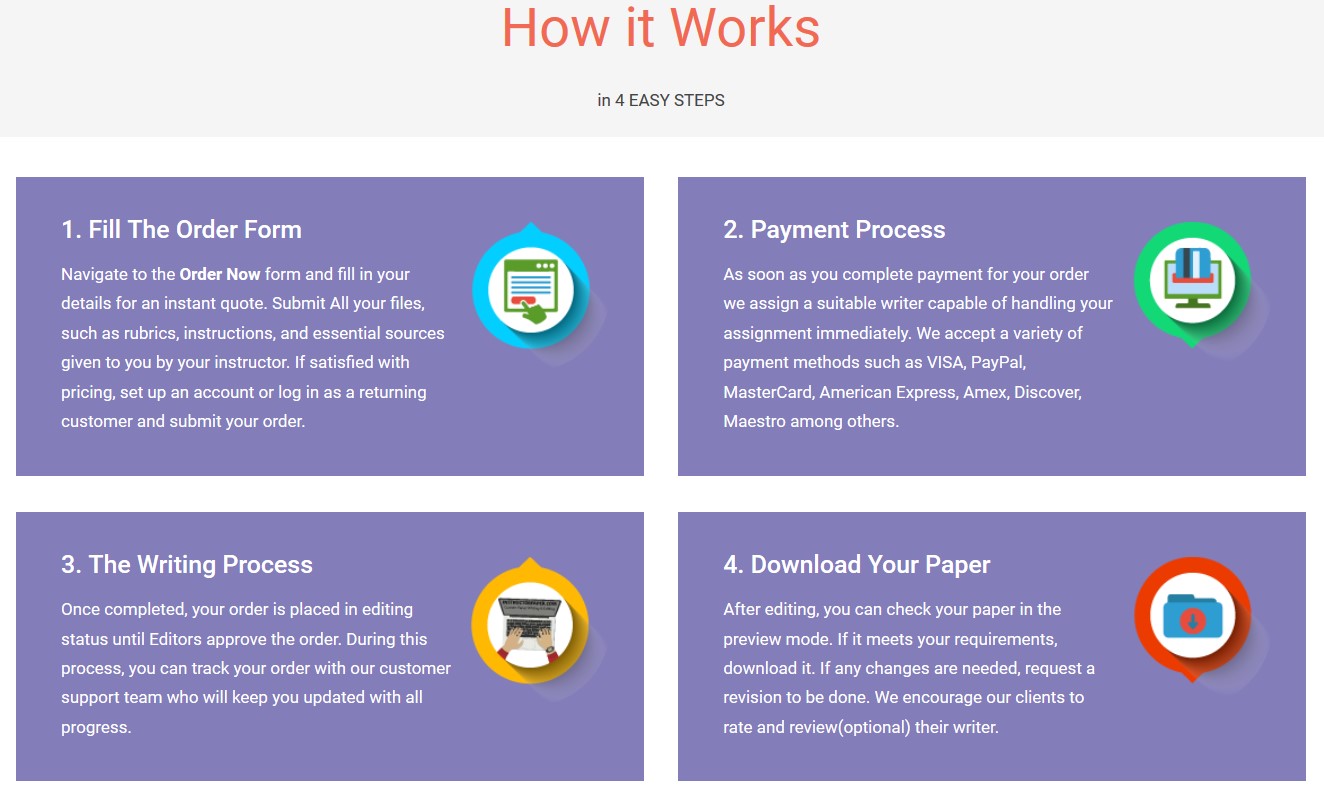
"If this is not the paper you were searching for, you can order your 100% plagiarism free, professional written paper now!"