Information Governance Security Function and Cybersecurity Paper
Reference:
1.) Smallwood, R. F. (2014). Information Governance: Concepts, Strategies, and Best Practices: John Wiley & Sons
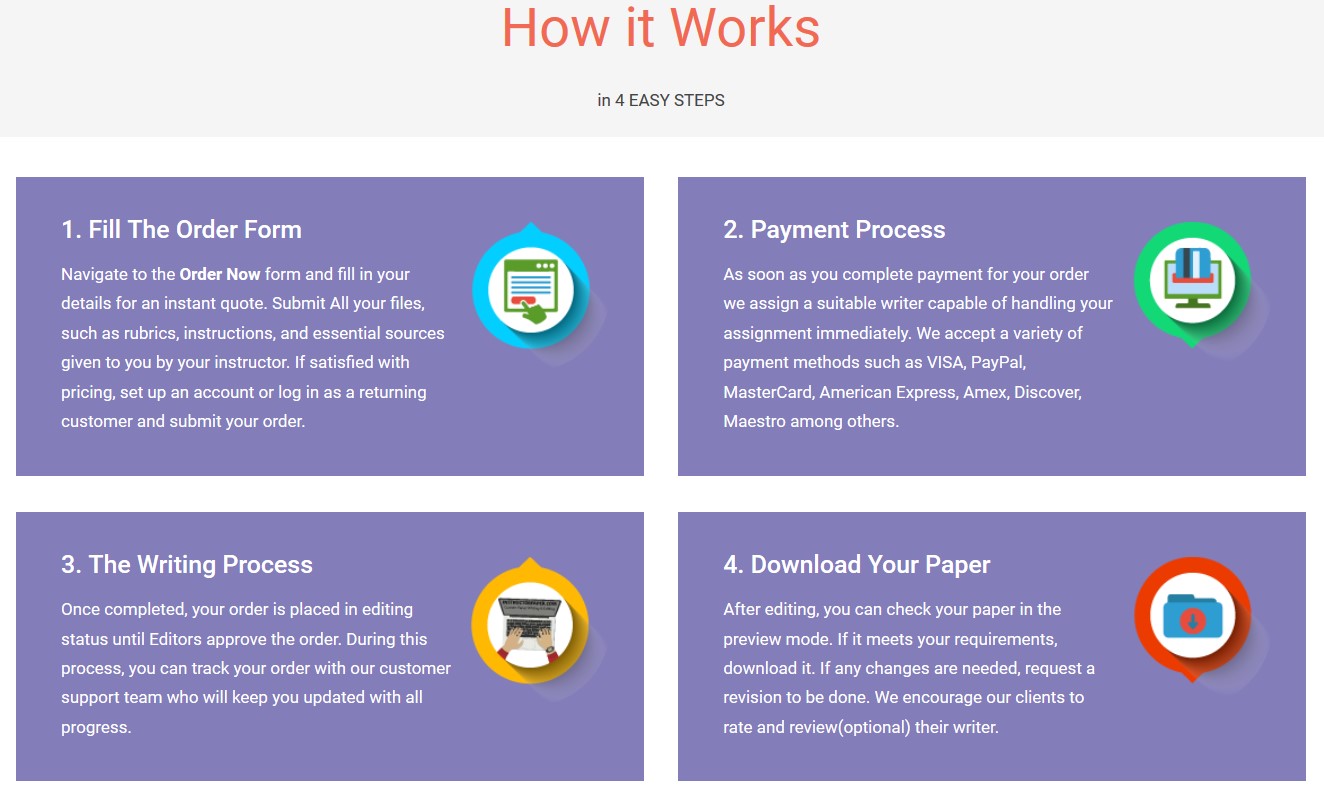
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper Now—–This week’s reading —- Read Chapter 11, from the textbook (Smallwood, 2014, pp. 207 – 238)..
Information Governance and Privacy and Security Function. Please answer and discuss the following:
1.- Where deleted files go?
2.- What do we mean with: Limitation of Perimeter Security?
3.- What is insider threat?
4.- Why in the work-place we need a strong and continues program of IG?
Support your finding with credible sources
Cite specific examples from this week’s readings and give credit to the source.
All submitted work must be per APA’s Style, Formatting and Structure.
Do not exceed 100 words per each answer.
The only reference that you must use this week is the:
Smallwood, R. F. (2014). Information Governance: Concepts, Strategies, and Best Practices: John Wiley & Sons.
NOTE: Don’t use or list any other reference. You must answer your questions only using your textbook.
==============================================================================================================
NOTE: Write Question 2 on a different word document.
2.) Also, Please discuss and submit your answer to the following question:
What do we mean when we say Cybersecurity?
What is Cybersecurity threat?
Why we need to implement methods and procedures to protect our personal information from Cyber-attacks?
What are the pros and cons?
==============================================================================================================
"If this is not the paper you were searching for, you can order your 100% plagiarism free, professional written paper now!"