Information Security System Plan
Information Security System Plan.
1. Use the following guidance to complete the System Security Plan using the template from Appendix A of NIST SP 800-18.
a. Sections 1 through 10 will contain information provided in the assigned case study. You may need to “interpret” that information when writing the descriptions. “Fill in the blanks” for information about the company or its managers which is not provided in the case study, i.e. names, email addresses, phone numbers, etc.). Make sure that your fictional information is consistent with information provided in the case study (name of company, locations, etc.).
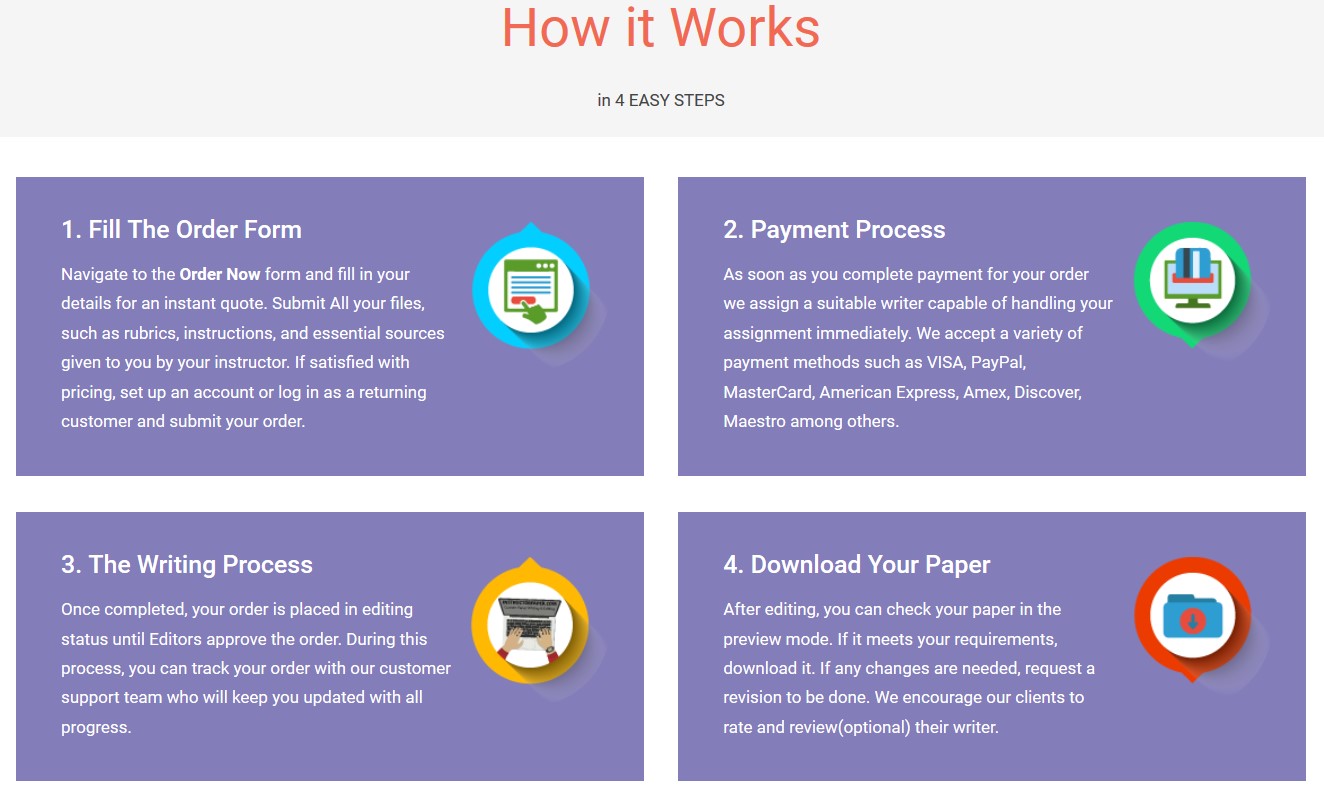
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper Nowb. Section 11 should contain information about the Wilmington, DE headquarters office’s Internet connection Do not include the table. Use the business Internet Services Provider listed at the top of this assignment file. Describe the system interconnection type in this section and service level agreement.
c. Section 12 should contain information derived from the case study. You will need to identify the types of information processed in the headquarters offices and then list the laws and regulations which apply. For example, if the case study company processes or stores Protected Health Information, then this section must include information about HIPAA. If the company processes or stores credit card payment information, then this section must include information about the PCI-DSS requirements. For the Headquarters Offices you also have financial information which may be covered by regulations issued by the Securities and Exchange Commission.
d. Section 13 of the SSP will take the most research and writing time. You MUST provide the required descriptive paragraphs for the three categories AND the explanations as to how the security controls within the control families will be used to secure the IT infrastructure. You MUST use the selected security control families and security controls as provided security controls baseline.
Information Security System Plan
"If this is not the paper you were searching for, you can order your 100% plagiarism free, professional written paper now!"