UOF Cumberlands Threat Modeling with Stride
UOF Cumberlands Threat Modeling with Stride.
We use many different types of risk management methodologies and tools. A part of the process involves identifying the threats to our system, generally by attackers who would harm our systems and data (assets). I’ve included a project that walks you through a simple threat modeling exercise, using STRIDE, which you will apply using a scenario, to understand the basic process.
1. Read the threat modeling article using STRIDE located at https://www.webtrends.com/blog/2015/04/threat-modeling-with-stride/ and complete a threat model and risk management plan
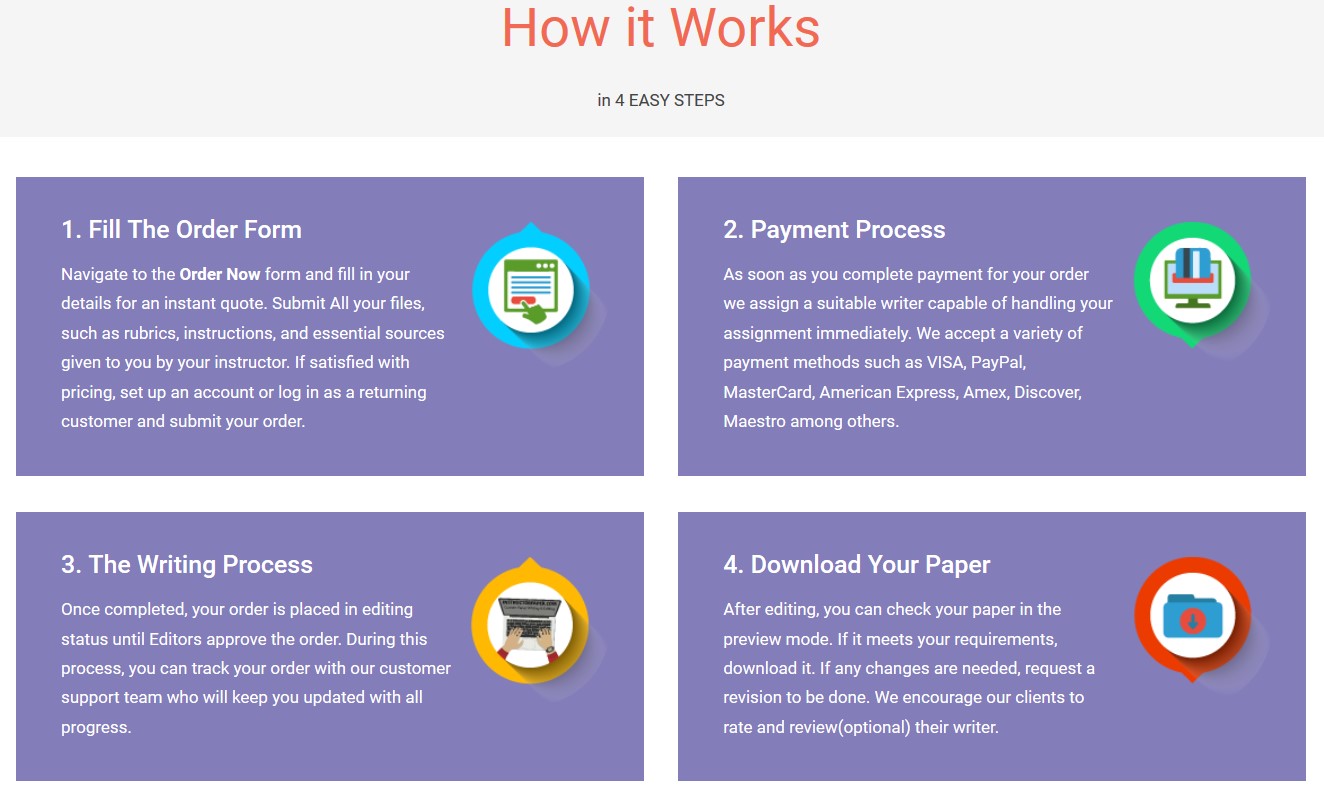
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper Now2. Read the attached Project description. you will create a report for your “boss” identifying the threats to your systems/assets in the scenario, who the attackers are, how they will attack (using STRIDE), and will make recommendations for security controls (use your textbook, too).
UOF Cumberlands Threat Modeling with Stride
"If this is not the paper you were searching for, you can order your 100% plagiarism free, professional written paper now!"