Subject: ITS-834: Emerging Threats & Countermeasures
Textbook Title: (ISC)2 CISSP Certified Information Systems Security Professional Official Study Guide ISBN: 9781119475958, Authors: Mike Chapple, James Michael Stewart, Darril Gibson, Publisher: John Wiley & Sons, Publication Date: 2018-04-10
Discussion: PKI and Cryptographic Applications
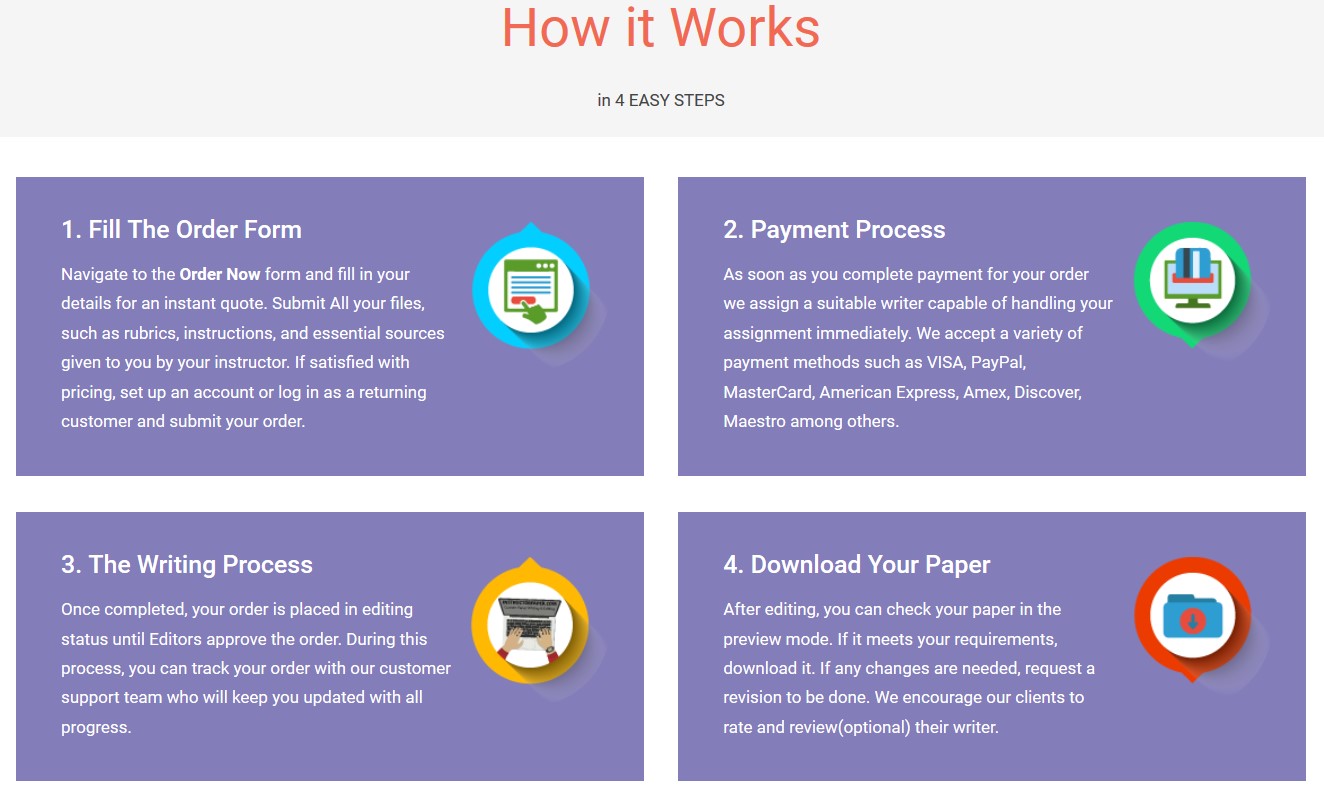
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper NowWord count: 300+ words
Chapters 6, 7, and 8 in the course textbook.
Malicious individuals have discovered several methods to attack and defeat cryptosystems. It’s important that understand the threats posed by cryptographic attacks to minimize the risks to your network systems.
Identify one cryptographic attack and how you can protect against it.
Make sure to back up your statements with scholarly support.
- Please cite properly in APA 7
- At least one scholarly source should be used.
- Use proper citations and references in your post.
Research Paper: Threat Modeling
Number of pages: 4+
A new medium-sized health care facility just opened and you are hired as the CIO. The CEO is somewhat technical and has tasked you with creating a threat model. The CEO needs to decide from 3 selected models but needs your recommendation. Review this week’s readings, conduct your own research, then choose a model to recommend with proper justifications. Items to include (at a minimum) are:
- User authentication and credentials with third-party applications
- 3 common security risks with ratings: low, medium or high
- Justification of your threat model (why it was chosen over the other two: compare and contrast)
You will research several threat models as it applies to the health care industry, summarize three models and choose one as a recommendation to the CEO in a summary with a model using UML Diagrams (Do not copy and paste images from the Internet). In your research paper, be sure to discuss the security risks and assign a label of low, medium or high risks and the CEO will make the determination to accept the risks or mitigate them.
Your paper should meet the following requirements:
- Four pages in length, not including the required cover page and reference page.
- Follow APA 7 guidelines. Your paper should include an introduction, a body with fully developed content, and a conclusion.
- Support your answers with the readings from the course and at least two scholarly journal articles to support your positions, claims, and observations, in addition to your textbook.
- Be clearly and well-written, concise, and logical, using excellent grammar and style techniques. You are being graded in part on the quality of your writing.
Note: plagiarism check required, APA7 format, include References, within 8hrs
This post has 2 individual assignments (a discussion and a research paper). Please provide answers in separate documents.
"If this is not the paper you were searching for, you can order your 100% plagiarism free, professional written paper now!"