Synthesize financial and business risk in order to develop long and short term strategic plans.
Synthesize financial and business risk in order to develop long and short term strategic plans..
Purpose
Information assets are constantly being attacked, and information security has become a high priority for organizations. The big question that many organizations are asking is how much security do they need? In short, organizations are struggling with finding the right amount of financial resources to invest in cybersecurity. What is the right investment for cybersecurity? Is more necessarily better when it involves protecting digital assets? Overinvesting in cybersecurity will reduce revenue and create unhappy shareholders, and underinvesting can have negative effects on the organization. In this assignment, you will evaluate risk and use financial tools to invest in security solutions. You will use several financial formulas.
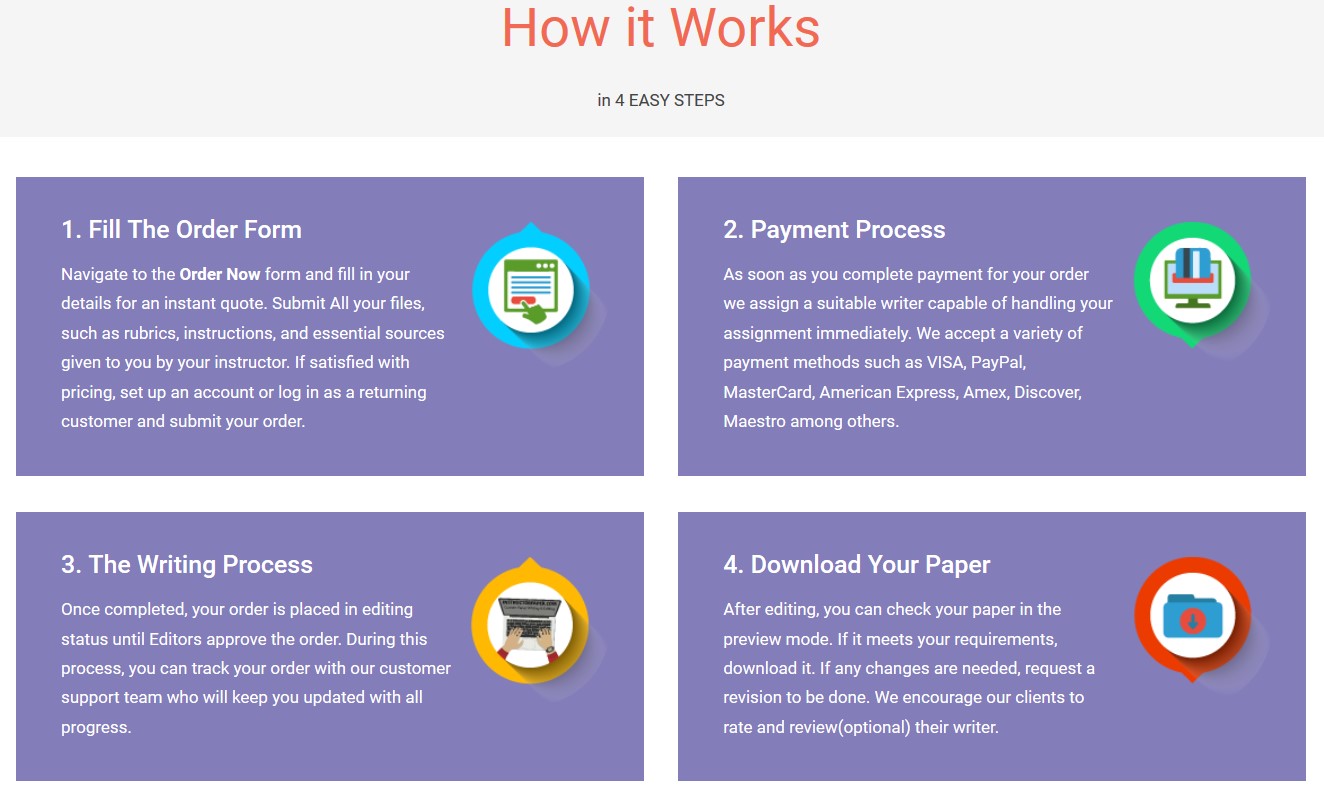
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper NowAssignment Instructions
For this Assignment, you will work through four mini-scenarios that consist of financial investing and risk identification.
Scenario 1: Return on Investment (ROI)
ROI is used to decide where to invest financial assets. The finance group of a company may use ROI to decide whether to fund project A or project B. The formula for calculating ROI is given below.

ArmCPU company manufactures memory chips. The company wants to expand production to a faster memory chip which will cost $2M. This new chip is expected to bring $6M over the next three years. What is the ROI? Use approximately 100 words to explain your answer.
Scenario 2: Return on Security Investment (ROSI)
Security investment is a little more complex. There are no tangible gains in investment directed at information security. The return is measured on risk avoidance. The formula for calculating ROSI is given below.

ArmCPU has been attacked by the BAD-VIRUS before. The damage as a result of the BAD-VIRUS in 2017 was $52,000 for all occurrences and all users. The implementation of an anti-virus solution was $25,000 for all of its users. The anti-virus solution worked 75% of the time on BAD-VIRUS.
Identify the following from the data given:
What is the Risk Exposure?
What is the percentage of risk mitigated?
How much did the solution Cost?
Compute ROSI?
Do think that anti-virus solution is worth the investment? Use approximately 150 words to explain your answer.
Scenario 3: Quantifying Risk Exposure
Before we look at an equation to calculate Risk Exposure (RE) on an annual basis (ALE), let me point out that the equation for Risk Exposure uses two variables – Single Lost Exposure (SLE) and Annual Rate of Occurrence (ARO). ALE is the product of these two variables. The equation for ALE is given below.
Suppose the ARO is 0.5 (once in two years) and the SLE is $10,000. Compute the ALE. Use approximately 50 words to explain what this value means.
Scenario 4: Complex Problem Using ALE
Definition of vulnerability, threat and risk of problem #4
- Vulnerability – No backup
- Threat – A Laptop failure
- Risk – Data Loss
What is the asset in this problem?
Suppose the asset is worth $50,000. The Single Lost Expectancy (SLE) is computed by multiplying the Actual Value by the Exposure Factor
In our case, the SLE = Actual Value (AV) X Exposure Factor (EF). The Exposure Factor is the loss that can occur as a result of the threat. For problem #4, we are going to assume that the SLE is $10,000.
What is EF?
We are going to keep the ARO (the frequency of the threat every year) as .5 assuming that the laptop crashes once every two years.
Compute the ALE. Remember 
Generally, the equation below is used to decide whether to implement a particular mitigation strategy
Mitigation Investment (M1) = ALE1 (before the Mitigation Investment) – ALE2 (after the Mitigation Investment) – Total Cost of implementing the mitigation strategy (TC).

Suppose the cost of completing and maintaining a backup for a laptop is $400 and the ALE2 is $1000. What should be the allowable investment for this security risk? Use approximately 200 words to explain your answer.
Assignment Requirements
In a Word® document, supply all of your answers for the scenarios given. Be sure to answer all questions. Cite all sources in APA style where applicable.
For more information on APA style formatting, go to APA Style Central under Academic Resources of this course or visit the Writing Center.
Also review the university policy on plagiarism. If you have any questions, please contact your professor.
Synthesize financial and business risk in order to develop long and short term strategic plans.
"If this is not the paper you were searching for, you can order your 100% plagiarism free, professional written paper now!"