Topic 2: Designing Cyberwarfare Defense Strategies. As noted in Theohary and Rollins (2015), trying to define what cyberwarfare actually is can be quite difficult. A large part of the problem in defining what constitutes cyberwarfare is the range of threat actors that engage in various cyberwarfare activities. Given a similar outcome of disruption either to a national government or a country’s infrastructure, discuss what differences there may be in defensive strategies that would depend on different threat actors. Consider the different motivations of different threat actors and how motivation might inform a particular defensive strategy.
Theohary, C., & Rollins, J. (2015, March 15). Cyberwarfare and cyberterrorism: In brief. Retrieved from http://fas.org/sgp/crs/natsec/R43955.pdf
Topic 2: Designing Cyberwarfare Defense Strategies
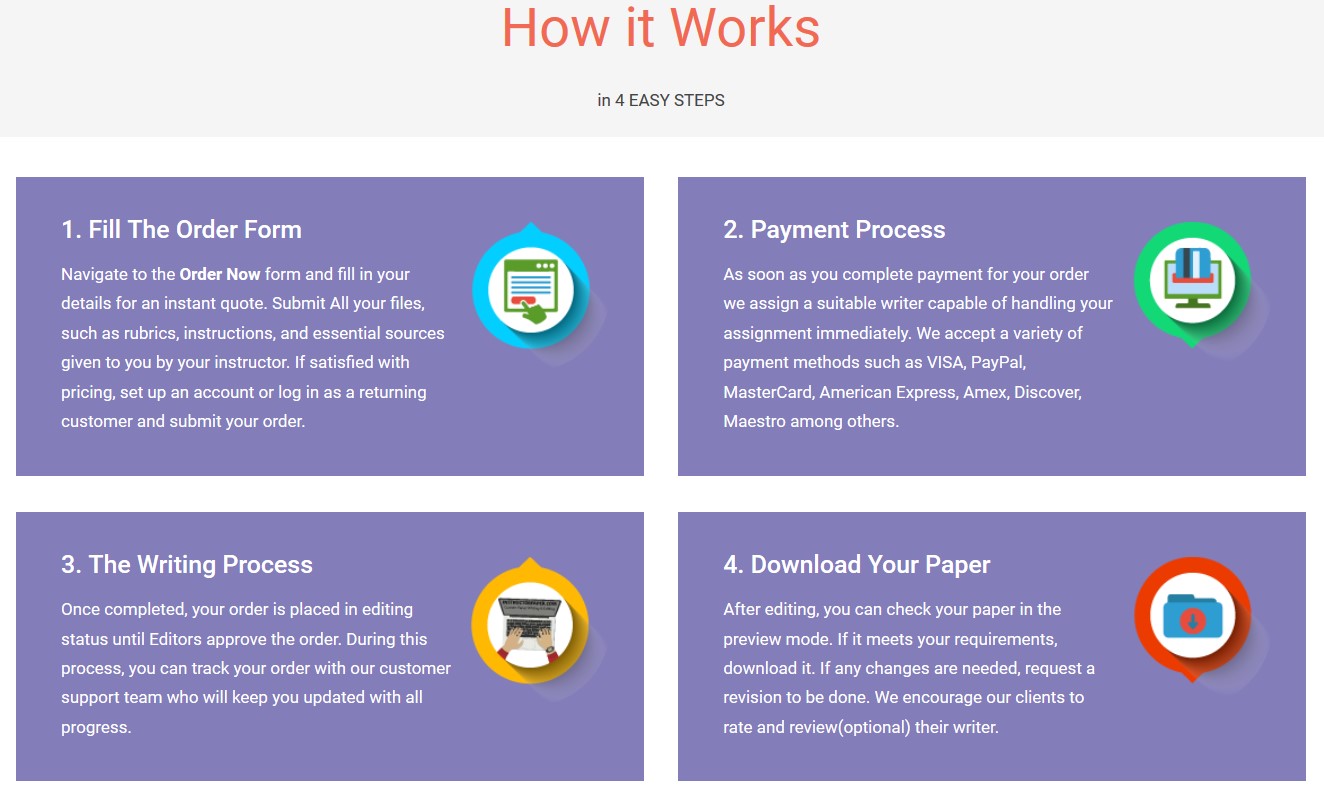
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper Now"If this is not the paper you were searching for, you can order your 100% plagiarism free, professional written paper now!"